This article was first published in Network Computing.
Ask a security professional to identify the weakest link in cybersecurity chain and they will likely give you the same answer: humans.
People respond to emails they shouldn’t open. They access services and websites they shouldn’t on corporate devices. They invite business partners that employ less-than-vigorous security procedures into their corporate networks
That’s true, but we all make mistakes. More importantly, today’s criminal is sophisticated, dedicated and patient. Hackers cost consumers and companies $375 billion to $575 billion a year, according to a study by the Center for Strategic and International Studies funded by McAfee. Core technology can be compromised too. In 2014, the FBI warned that hackers were targeting healthcare and medical device companies for intellectual property.
So what can be done? Security never ends and it’s never perfect — that’s the ultimate reality. But it can be improved. And one avenue for improving it will be relying increasingly on automated encryption. Encryption is arguably the best security technology on the market and one of the least used. Think of it. Your tax returns are probably on a drive somewhere in your house. Have you encrypted them? Probably not. Could someone read them if they stole your laptop and cracked the password? Absolutely.
Like anything else, encryption can be hacked, but it often takes money, time and brute force computing. Encryption may not have prevented the recent spate of high-profile attacks, but it could have prevented the sudden onrush of embarrassing emails, usernames and other information. The perpetrators would likely still be struggling with strings of jibberish.
“Encryption should be enabled for everything by default, not a feature you turn on only if you’re doing something you consider worth protecting,” security expert Bruce Schneier wrote in his blog.
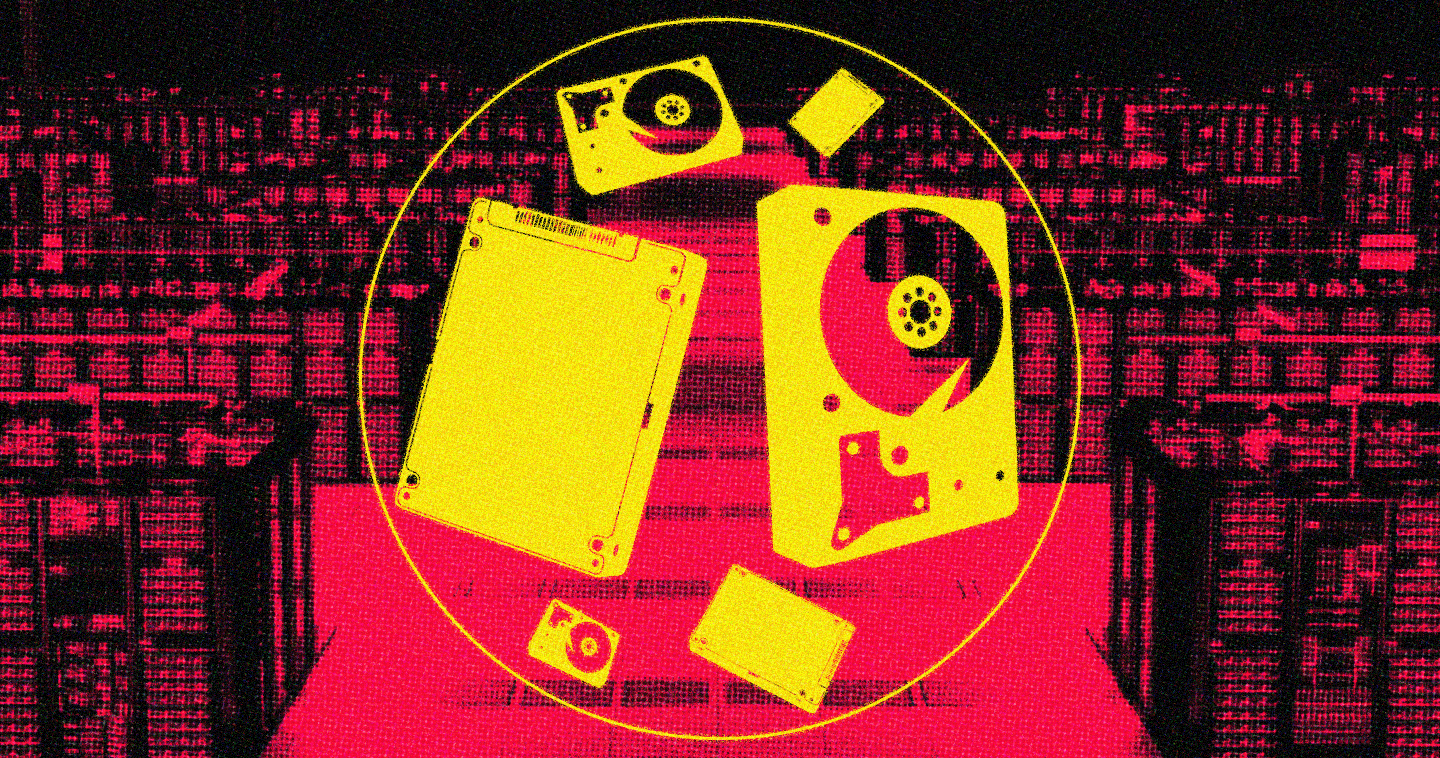
Until relatively recently, however, the cost and complexity involved made encryption a nonstarter for most. Third-party services that simplify encryption are perceived by some to be less secure. The escalating capabilities of computing systems, however, are changing the picture by eliminating performance and cost barriers. For example, the speed and capacity of solid-state drives (SSDs) allows encryption to take place behind the scenes.
Coughlin Associates predicts that by the end of the year the majority of SSDs will be capable of self-encrypting documents. Nuvasive, a company that specializes in spinal care technology, recently implemented a self-encryption program through SSDs.
Regulatory changes are also encouraging adoption under Sarbanes-Oxley, the Healthcare Information Portability and Accountability Act (HIPAA ), the Health Information Technology for Economic and Clinical Health (HITECH) Act ,and other regulations. In 2009, BlueCross BlueShield of Tennessee was fined $1.5 million (and spent $17 million in remedial actions) after 57 unencrypted hard drives containing records for nearly one million patients were stolen from a storage closet. An estimated 249,000 records were inadvertently exposed last year because of lost or stolen laptops, according to statistics from Privacy Rights Clearinghouse.
Applications for managing encryption or setting policies are also becoming far more user-friendly. All the ingredients needed for “one-touch” encryption will soon be difficult not to get in a new system. Companies like Wave, for instance, allow encryption to be implemented on laptops automatically or through the cloud. (Encryption can also be confined to specific folders to make it even easier.)
The large web services, meanwhile, are adopting automated encryption. Google employs an encrypted connection for Gmail and is moving toward “end-to-end” encryption that will effectively keep messages encrypted until the intended recipient unscrambles them.
You’re also seeing encryption and better security percolate into the mobile market. China’s Qiku has released phones that emphasize security. Earlier this year, Google showed off its experimental Project Vault, a microSD-sized card that keeps mobile messages and data secure.
Critics and skeptics will note that even making encryption capabilities free and pervasive may not be enough. Still, things can change quickly. If you make encryption as easy as clicking an icon or completely automatic, attitudes will change. For close to 20 years, a veritable armada of companies tried to promote fingerprint scanners as a password replacement, but few adopted them. Then Apple put fingerprint systems on the iPhone 5. Suddenly, users adopted the technology and were asking what took so long.