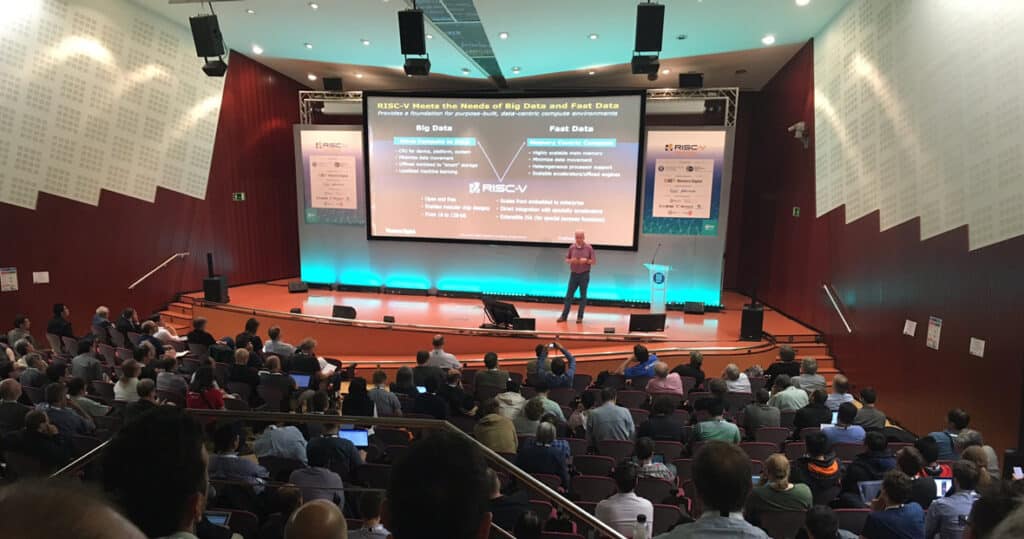
From the world’s largest data centers, to the smallest RISC-V device, and the future of edge computing – the first day of the RISC-V Workshop was exciting!
If you’re not familiar with RISC-V, it is an open, free instruction set architecture (ISA) that will enable a new era of processor innovation and computing design. It is a movement that is gaining great momentum. We, too, are RISC-V Foundation members. Just a few months ago Western Digital announced that we’re transitioning our own consumption of processors – over one billion cores per year – to RISC-V.
So how far has RISC-V come, what impact will it have and why should you care? Here are our five takeaways from the first day of the RISC-V Workshop (visit the RISC-V website for full recaps of all sessions and presentations).
1) Innovation = Customization
The premise for the RISC-V movement is that instruction sets want to be free. Why? Because most of today’s processor architectures are designed for general-purpose workloads. Yet workloads are no longer uniform.
Big Data and Fast Data applications require very different types of architectures for how data is stored, accessed and transformed, whether at core, cloud or edge data centers. Extreme workloads (such as analytics, machine learning, artificial intelligence and smart systems) need to focus on the requirements of data, with optimized levels of OS processing, specialty processing, memory, storage and interconnect.
The open source movement has demonstrated that innovation can be maximized with a large community working toward a common goal. Open source innovation often happens at a much faster pace, and can be far more focused on customer needs than when a proprietary model is used. RISC-V can democratize compute architecture and enable the creation of custom silicon without requiring an overwhelming investment or a high-volume guarantee.
2) Hardware is from Venus, Software is from Mars
Open source has proven its technical and business benefits in the software world. The software world also has community standards and norms for licensing and using the source code of Open-Source Software (OSS) applications. However, the world of hardware is a different animal altogether.
For example, new software applications are built on easy to use cloud infrastructures that can quickly scale to millions of users. Yet with hardware you would need to manufacture 1 million chips to reach this many users… Manufacturing costs money, it takes time, and, unlike software, once you manufacture a chip you cannot change it.
Another key challenge when it comes to hardware and potential commercial uses of RISC-V is around IP and patents. Traditional licenses don’t quite apply to this world. Hardware design comes with potential threats of patent infringement or even lawsuits. This will require new approaches, as addressed by Martin Fink, Western Digital’s CTO, in his keynote session, to building open source hardware licensing that can ensure an open ecosystem.

3) A World of Embedded Possibilities
With everything from fitness trackers, to intelligent homes, or autonomous vehicles, it’s not hard to imagine how by 2020 the installed base of the Internet of Things (IoT) devices is forecast to grow to almost 31 billion worldwide.
As we imagine next-generation edge computing use cases, there are many IoT devices that could potentially do processing at the device level without the need to send data to be processed elsewhere. These would often be very narrow tasks that could be supported by an extremely small, ultra low power and low-cost processors.
This concept of bringing compute to data, rather than data to compute, allows for more intelligent infrastructures and removes the costs and latency of interconnect bandwidth.
Western Digital CTO, Martin Fink, explains why Western Digital is using this open architecture:
4) Adoption is Real
The adoption of RISC-V is explosive. The RISC-V Foundation was established in 2015. In early 2016 there were about 16 members. Today there are over 150 members comprising the foundation! The more than two dozen poster sessions and announcements were a great view into the incredibly diverse work done around, and with, RISC-V today.
Western Digital is advancing our efforts around RISC-V implementation and are currently working on our first two cores. We will share more about our advancements on this blog over the next weeks and months.
5) No Need to Be in the Processing Business to Care
Although we are very interested in RISC-V, Western Digital is not getting into the processing business, and you don’t need to, either. We care about open ISA because it impacts what our customers can do with their data. We see an ecosystem that can jointly deliver better architectures from edge, to core, to cloud.
Millions of users and businesses around the world have entrusted us with their data. We are in a great position to help them realize its full potential and value. RISC-V matters because open source innovation democratizes compute architecture, allowing us to do what we do best — create environments where data can thrive, so our customers can thrive.
Forward-Looking Statements
Certain blog and other posts on this website may contain forward-looking statements, including statements relating to expectations for our product portfolio, the market for our products, product development efforts, and the capacities, capabilities and applications of our products. These forward-looking statements are subject to risks and uncertainties that could cause actual results to differ materially from those expressed in the forward-looking statements, including development challenges or delays, supply chain and logistics issues, changes in markets, demand, global economic conditions and other risks and uncertainties listed in Western Digital Corporation’s most recent quarterly and annual reports filed with the Securities and Exchange Commission, to which your attention is directed. Readers are cautioned not to place undue reliance on these forward-looking statements and we undertake no obligation to update these forward-looking statements to reflect subsequent events or circumstances.